Application Security in a cloud environment such as Amazon EC2
By: Emilley J in Cloud Tutorials on 2012-10-20
In addition to the inbuilt security of any IAAS architecture such as Amazon EC2, the application itself should enforce security between its webservers, application servers and database servers. This is achieved by the use of Security Groups and grouping the servers in their own security groups. This is explained in the diagram below.
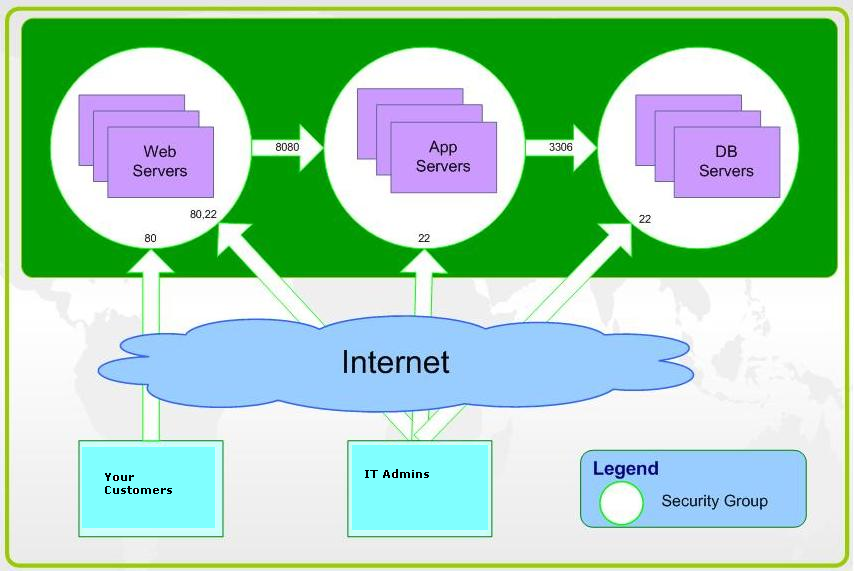
The three tier architecture is replicated in Amazon EC2 by the use of Security Groups . Three different security groups should be created in the Amazon EC2.
- Webservers group
In this group the websites together with any UI servers will be hosted. Any other server that is open to the public should be added to this group. This group is equivalent to the DMZ zone in a traditional network architecture. Port 80 will be opened in this group.
- Appservers group
The Appserver's group will consists of all the Appservers in your application such as SSO server, Monitoring Server, etc. This group is protected with specific ports and only accessible from the webserver group of instances.
- DB Servers group
This group hosts the hot and standby Database Servers and only the port 3306 or 1433 based on which database you use, is open to be accessed from the Appserver group.
The IT Admin staff will be able to remotely manage the servers via SSH or RDP based on your platform.
Add Comment
This policy contains information about your privacy. By posting, you are declaring that you understand this policy:
- Your name, rating, website address, town, country, state and comment will be publicly displayed if entered.
- Aside from the data entered into these form fields, other stored data about your comment will include:
- Your IP address (not displayed)
- The time/date of your submission (displayed)
- Your email address will not be shared. It is collected for only two reasons:
- Administrative purposes, should a need to contact you arise.
- To inform you of new comments, should you subscribe to receive notifications.
- A cookie may be set on your computer. This is used to remember your inputs. It will expire by itself.
This policy is subject to change at any time and without notice.
These terms and conditions contain rules about posting comments. By submitting a comment, you are declaring that you agree with these rules:
- Although the administrator will attempt to moderate comments, it is impossible for every comment to have been moderated at any given time.
- You acknowledge that all comments express the views and opinions of the original author and not those of the administrator.
- You agree not to post any material which is knowingly false, obscene, hateful, threatening, harassing or invasive of a person's privacy.
- The administrator has the right to edit, move or remove any comment for any reason and without notice.
Failure to comply with these rules may result in being banned from submitting further comments.
These terms and conditions are subject to change at any time and without notice.
- Data Science
- Android
- React Native
- AJAX
- ASP.net
- C
- C++
- C#
- Cocoa
- Cloud Computing
- HTML5
- Java
- Javascript
- JSF
- JSP
- J2ME
- Java Beans
- EJB
- JDBC
- Linux
- Mac OS X
- iPhone
- MySQL
- Office 365
- Perl
- PHP
- Python
- Ruby
- VB.net
- Hibernate
- Struts
- SAP
- Trends
- Tech Reviews
- WebServices
- XML
- Certification
- Interview
categories
Related Tutorials
Power On a VM from ESXI command line
How to change the virtual machine name in Azure
Install OpenStack step by step guide
How to get the API key for CloudStack
HA and DR in a cloud environment such as Amazon EC2
Backup and recovery in a cloud environment such as Amazon EC2
Application Security in a cloud environment such as Amazon EC2
Comments